South Africa’s creators, coders and founders are under pressure to do more with less. Whether you’re running a meme page from Mitchells Plain, debugging…
Jailbreak any iOS device with ‘Malicious Chargers’ says Black Hat specialist
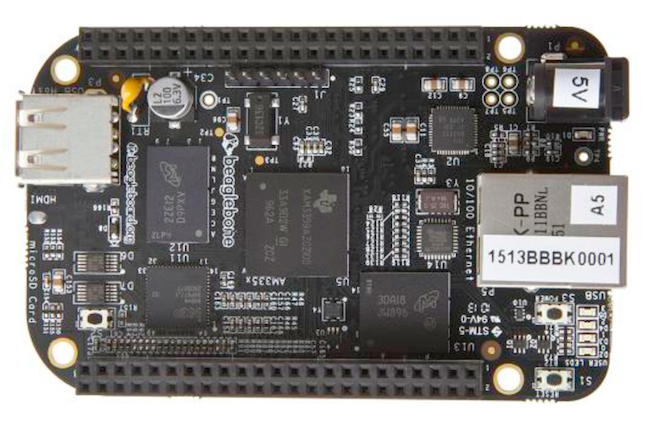
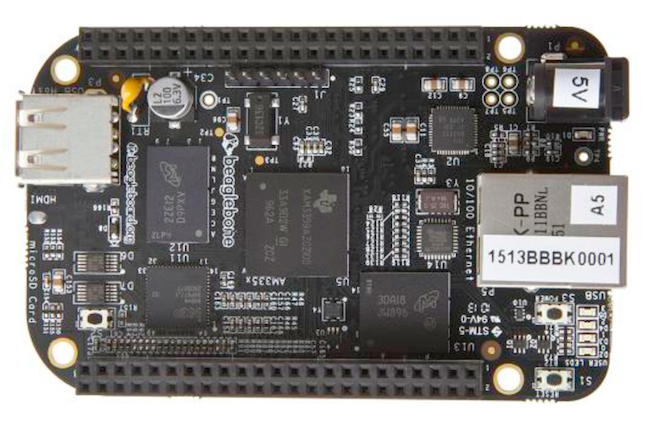
There’s one event held every year that we should all be aware of, and that’s the hacker-focused Black Hat conference. This years US conference which kicks off 27 July (there are Black Hat events in Europe and the UAE as well) will expose this gem: that any iOS device can be hacked in minutes with “malicious chargers” called Mactans, which are in turn controlled by a Rasberry Pi-like computer called a BeagleBoard. But again, it’s a plug-and-hack solution for any iPhone, iPod, iPad or iToilet.
The hacker’s presenting at the iOS Black Hat talk say that their tests were “alarming.” One of the speakers, Billy Lau of the Georgia Institute of technology discusses his initial findings and what will go down during his presentation.
despite the plethora of defense mechanisms in iOS, we successfully injected arbitrary software into current-generation Apple devices running the latest operating system (OS) software. All users are affected, as our approach requires neither a jailbroken device nor user interaction.
The Mactans is plugged into an iOS device and it’s “compromised within one minute of being plugged in.” The device and the team quickly get to work by analyzing the iOS security mechanisms which blocks unsupported apps. The team then leverages the USB capabilities of the Mactans to counteract all Apple software defenses. The results are that any software can be hidden in the same manner in which Apple masks its own proprietary applications and in turn, any application cam be installed.
Here’s possibly the scariest part of the iOS hacking talk — the Mactans,the malicious USB charger, was built with very little time and money. “Consider what more motivated, well-funded adversaries could accomplish?” says the iOS hacking team. This years US-based Black Hat conference takes place at Ceasers Palace, Nevada, Las Vegas from 27 July – 1 August.
Jailbreaking an iOS device isn’t the trickiest affair, but it brings with it the risk of a “bricked” device. The malicious charger slides any app into an iOS device without having to trick the operating system. We’ll discover more when the iOS hacking team takes apart Apple’s security systems at the US Black Hat hacking conference.


